Google has done more for the world, than any other company I can think of. It is easy to blame “big tech” companies for all that is wrong – and as I write, there is a very visible protest against Facebook – but the truth is that “humans are only humans”. We will always find ways to misuse contents and technology in general, refuse to take the blame, and then ask others for solutions.
This constantly happens, at very different scales. Parents, religious groups, organizations of different shapes and forms, blame what they think is “wrong” with their kids, affiliates, members, etc., on the music they listen, the movies they watch, the books they read, the apps they use; the people they communicate with, the news they (do not) read, etc.
The opportunity to, alternatively, take a good introspective look at the mirror, is rarely taken. It is easier to find scapegoats.
These companies and ad agencies that, today, are taking the hypocritical path against Facebook, will do it to Google, to your company, or to yourself (!) tomorrow. They are oversimplifying extremely complex social questions and, with that, doing more harm than good. Our world is not trivial. Isolated hashtag reactions are some of what is wrong in human behavior. It is required to go beyond the hashtag.
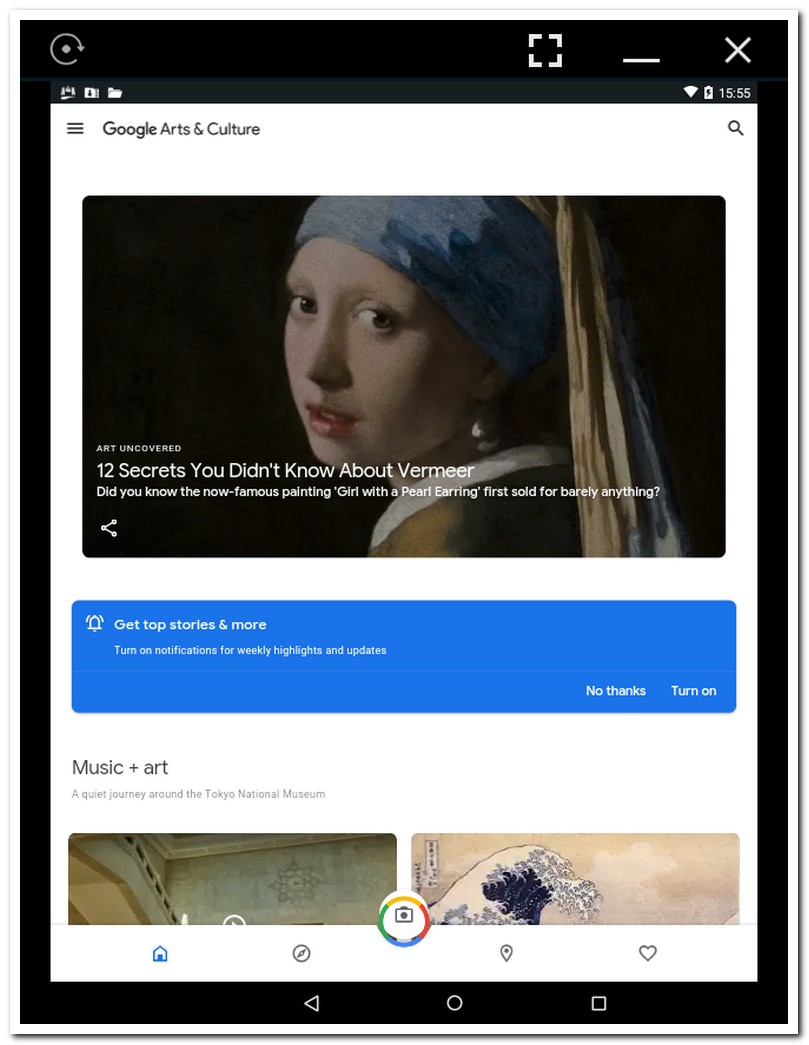
This post is about one of the many wonderful products and services that Google offers. It is not about “search”, “Gmail”, “Classroom”, “Maps”, “Earth”, “Android”, etc., but about something less known, yet equally relevant and loveable: the “Google Arts and Culture” app.
Of course, with the current trends, it is only a matter of time before one of these wonderful offerings to become under negative scrutiny, either because someone will find horrible things when searching, have sensitive data compromised, or encounter “indecent art”.
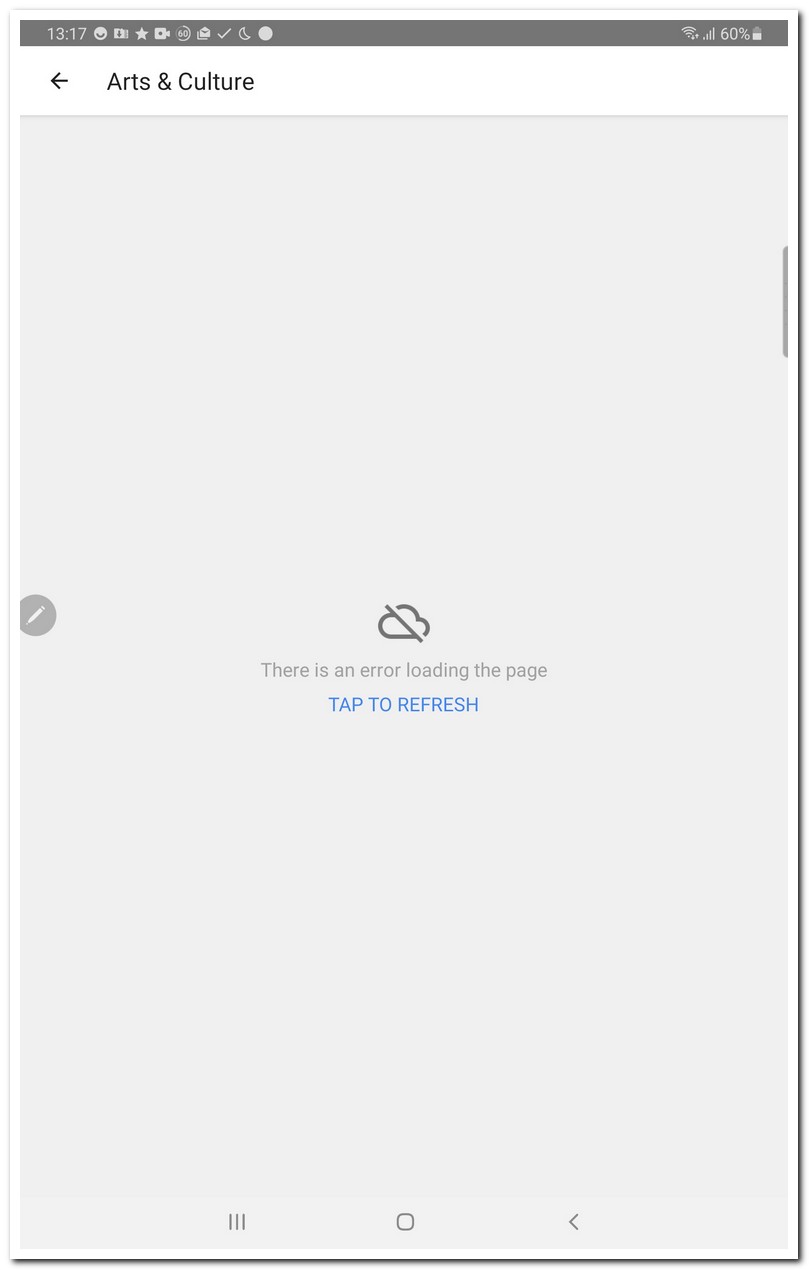
So, enjoy the “Arts” app while you can, if you can. I could NOT, until understanding and fixing the “tap to refresh” issue. This issue consists in a blank screen telling you to “tap to refresh”, to no avail.
The “Google Arts and Culture” app, is a wonderful effort, to help people learn about, and connect with arts and culture. In many countries, it will be localized enough, to be based on the local arts/culture. Unfortunately, in my case, the app did not work at all: it would launch, display a “tap to refresh” message, and systematically fail on every attempt to continue.
I investigated enough of the app behavior, to understand that the failure was because of the unavailability of certain network resources:
(1)
I had my filtering proxy configured to ignore http(s) requests matching the pattern
*.ggpht.com
, which in the past served me well, to block certain image-based ads. If I want to use the app, as it is, I must unblock that pattern.
(2)
A second network resource that must be unblocked, for the app to work, is the domain
google-analytics.com
. In my case, I had configured my private DNS to translate requests matching
*.google-analytics.*
to 0.0.0.0, not to the real IP address. Again, that served me well, for many years, not only against ads, but mostly against a plethora of user-behavior tracking techniques. In this case, I am disappointed of having to unblock google-analytics. In the future, I will research for a different solution.
Doing (1) and (2) enables the app “Google Arts and Culture” to function.
Technical Details
- ./ups/2020-07/05/ARTURMARQUES_DOT_COM_WP_AMAM/google_arts_and_culture_00_permissions_768.jpg
- attachment_id : 1079
- date_created_gmt : 2020-07-05 18:06:02
- parent : 0
- link : https://arturmarques.com/wp/wp-content/uploads/2020/07/google_arts_and_culture_00_permissions_768.jpg
- title : google_arts_and_culture_00_permissions_768.jpg
- caption :
- description :
- metadata :
- width : 809
- height : 1045
- file : 2020/07/google_arts_and_culture_00_permissions_768.jpg
- sizes :
- medium :
- file : google_arts_and_culture_00_permissions_768-232×300.jpg
- width : 232
- height : 300
- mime-type : image/jpeg
- large :
- file : google_arts_and_culture_00_permissions_768-793×1024.jpg
- width : 793
- height : 1024
- mime-type : image/jpeg
- thumbnail :
- file : google_arts_and_culture_00_permissions_768-150×150.jpg
- width : 150
- height : 150
- mime-type : image/jpeg
- medium_large :
- file : google_arts_and_culture_00_permissions_768-768×992.jpg
- width : 768
- height : 992
- mime-type : image/jpeg
- post-thumbnail :
- file : google_arts_and_culture_00_permissions_768-672×372.jpg
- width : 672
- height : 372
- mime-type : image/jpeg
- twentyfourteen-full-width :
- file : google_arts_and_culture_00_permissions_768-809×576.jpg
- width : 809
- height : 576
- mime-type : image/jpeg
- medium :
- image_meta :
- aperture : 0
- credit :
- camera :
- caption :
- created_timestamp : 0
- copyright :
- focal_length : 0
- iso : 0
- shutter_speed : 0
- title :
- orientation : 0
- keywords :
- type : image/jpeg
- thumbnail : https://arturmarques.com/wp/wp-content/uploads/2020/07/google_arts_and_culture_00_permissions_768-150×150.jpg
- id : 1079
- file : google_arts_and_culture_00_permissions_768.jpg
- url : https://arturmarques.com/wp/wp-content/uploads/2020/07/google_arts_and_culture_00_permissions_768.jpg
- ./ups/2020-07/05/ARTURMARQUES_DOT_COM_WP_AMAM/google_arts_and_culture_app_03_running_768.jpg
- attachment_id : 1080
- date_created_gmt : 2020-07-05 18:06:05
- parent : 0
- link : https://arturmarques.com/wp/wp-content/uploads/2020/07/google_arts_and_culture_app_03_running_768.jpg
- title : google_arts_and_culture_app_03_running_768.jpg
- caption :
- description :
- metadata :
- width : 809
- height : 1045
- file : 2020/07/google_arts_and_culture_app_03_running_768.jpg
- sizes :
- medium :
- file : google_arts_and_culture_app_03_running_768-232×300.jpg
- width : 232
- height : 300
- mime-type : image/jpeg
- large :
- file : google_arts_and_culture_app_03_running_768-793×1024.jpg
- width : 793
- height : 1024
- mime-type : image/jpeg
- thumbnail :
- file : google_arts_and_culture_app_03_running_768-150×150.jpg
- width : 150
- height : 150
- mime-type : image/jpeg
- medium_large :
- file : google_arts_and_culture_app_03_running_768-768×992.jpg
- width : 768
- height : 992
- mime-type : image/jpeg
- post-thumbnail :
- file : google_arts_and_culture_app_03_running_768-672×372.jpg
- width : 672
- height : 372
- mime-type : image/jpeg
- twentyfourteen-full-width :
- file : google_arts_and_culture_app_03_running_768-809×576.jpg
- width : 809
- height : 576
- mime-type : image/jpeg
- medium :
- image_meta :
- aperture : 0
- credit :
- camera :
- caption :
- created_timestamp : 0
- copyright :
- focal_length : 0
- iso : 0
- shutter_speed : 0
- title :
- orientation : 0
- keywords :
- type : image/jpeg
- thumbnail : https://arturmarques.com/wp/wp-content/uploads/2020/07/google_arts_and_culture_app_03_running_768-150×150.jpg
- id : 1080
- file : google_arts_and_culture_app_03_running_768.jpg
- url : https://arturmarques.com/wp/wp-content/uploads/2020/07/google_arts_and_culture_app_03_running_768.jpg
- ./ups/2020-07/05/ARTURMARQUES_DOT_COM_WP_AMAM/google_arts_and_culture_app_02_tap_to_refresh_768.jpg
- attachment_id : 1081
- date_created_gmt : 2020-07-05 18:06:08
- parent : 0
- link : https://arturmarques.com/wp/wp-content/uploads/2020/07/google_arts_and_culture_app_02_tap_to_refresh_768.jpg
- title : google_arts_and_culture_app_02_tap_to_refresh_768.jpg
- caption :
- description :
- metadata :
- width : 809
- height : 1270
- file : 2020/07/google_arts_and_culture_app_02_tap_to_refresh_768.jpg
- sizes :
- medium :
- file : google_arts_and_culture_app_02_tap_to_refresh_768-191×300.jpg
- width : 191
- height : 300
- mime-type : image/jpeg
- large :
- file : google_arts_and_culture_app_02_tap_to_refresh_768-652×1024.jpg
- width : 652
- height : 1024
- mime-type : image/jpeg
- thumbnail :
- file : google_arts_and_culture_app_02_tap_to_refresh_768-150×150.jpg
- width : 150
- height : 150
- mime-type : image/jpeg
- medium_large :
- file : google_arts_and_culture_app_02_tap_to_refresh_768-768×1206.jpg
- width : 768
- height : 1206
- mime-type : image/jpeg
- post-thumbnail :
- file : google_arts_and_culture_app_02_tap_to_refresh_768-672×372.jpg
- width : 672
- height : 372
- mime-type : image/jpeg
- twentyfourteen-full-width :
- file : google_arts_and_culture_app_02_tap_to_refresh_768-809×576.jpg
- width : 809
- height : 576
- mime-type : image/jpeg
- medium :
- image_meta :
- aperture : 0
- credit :
- camera :
- caption :
- created_timestamp : 0
- copyright :
- focal_length : 0
- iso : 0
- shutter_speed : 0
- title :
- orientation : 0
- keywords :
- type : image/jpeg
- thumbnail : https://arturmarques.com/wp/wp-content/uploads/2020/07/google_arts_and_culture_app_02_tap_to_refresh_768-150×150.jpg
- id : 1081
- file : google_arts_and_culture_app_02_tap_to_refresh_768.jpg
- url : https://arturmarques.com/wp/wp-content/uploads/2020/07/google_arts_and_culture_app_02_tap_to_refresh_768.jpg